Expert articles, news and guides from the world of telecommunications and IT security.

Business internet with backup is not a double-cost solution — it is an architecture combining primary FTTO fiber connection with automatic LTE-A Pro or 5G backup via eSIM. The result is availability exceeding 99.9% and automatic failover within 10 seconds without manual intervention. A guide for IT managers: how to design backup correctly, what to require from the contract, and when to add a third layer of redundancy.
Read article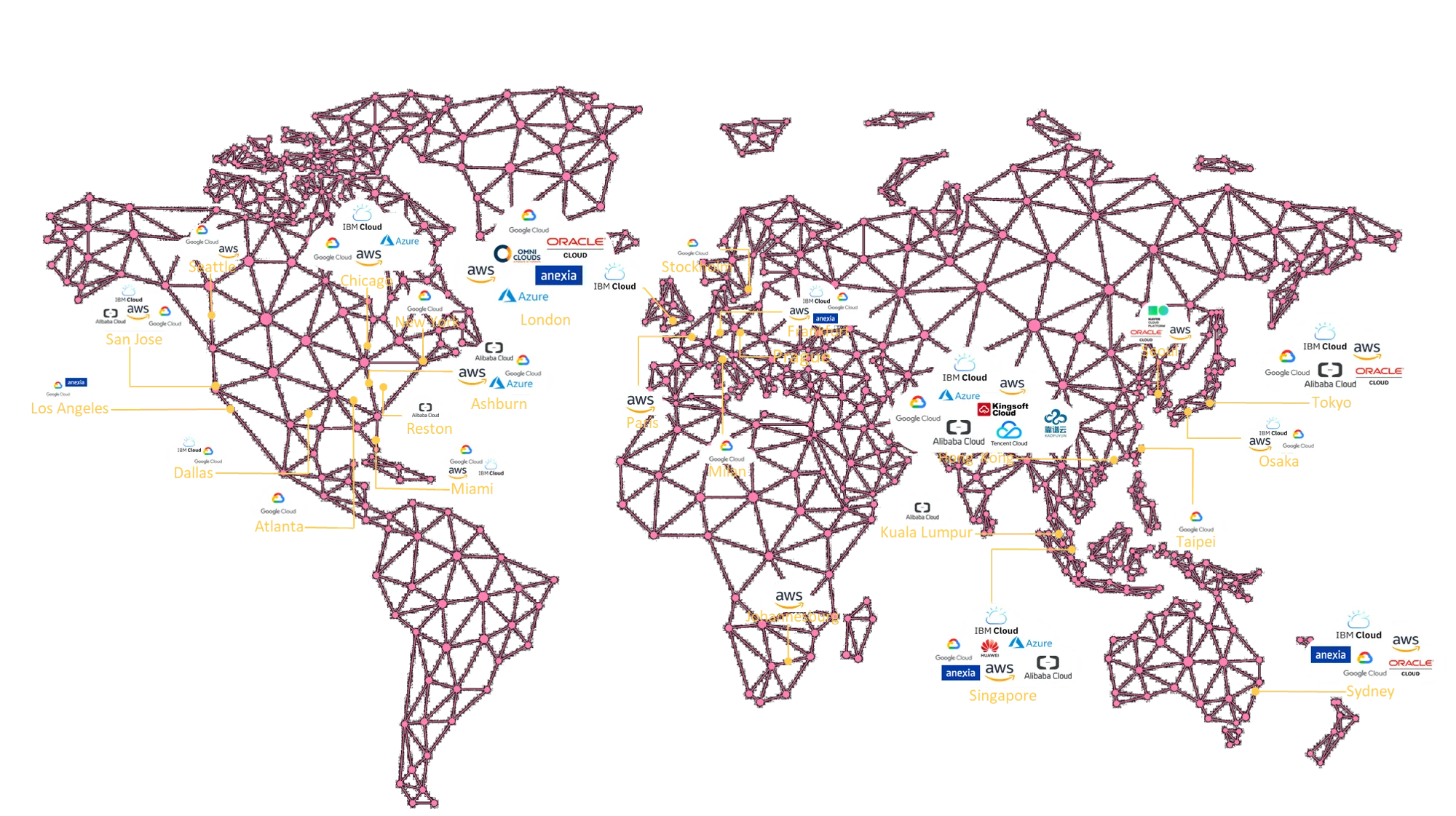
A private cloud link via CloudConnect enabled a holding company with three entities in Prague and Ostrava to consolidate access to AWS and Microsoft Azure under a single private MPLS VPN path — without public internet, with guaranteed latency, and 44% savings on egress costs. One port, three companies, two clouds.
Read article
New Telekom implemented for a medium-sized manufacturing company in Brno a guaranteed symmetrical business internet connection of 500 Mbit/s on FTTO fiber with automatic LTE-A Pro backup connectivity via eSIM. The result: 99.9% SLA, failover within 10 seconds, and zero unplanned outages in the first six months of operation.
Read article
Business internet is not an accelerated home tariff — it is guaranteed symmetrical connectivity with SLA, dedicated 1:1 capacity, direct peering at NIX.CZ, and 24/7 technical support. A guide for IT managers and operations directors: what distinguishes true B2B internet from commercial connections, which parameters to require, and when to switch to FTTO fiber.
Read article
A dedicated private cloud link is not just a technical preference — for an e-commerce platform transferring hundreds of TB of data monthly between its own data center and Microsoft Azure, it is a direct condition of availability and operational economics. New Telekom implemented a CloudConnect private circuit with 2 Gbit/s capacity, redundant last mile, and automatic failover — and reduced total egress traffic costs by 47%.
Read article
Business internet, dedicated MPLS VPN circuits between three locations, and a CloudConnect private line to Microsoft Azure — this is the network architecture designed and operated by New Telekom for an industrial manufacturer with headquarters in Prague, a manufacturing plant in the Central Bohemian Region, and a branch in Munich. One operator, one contract, three locations in two countries.
Read article
New Telekom provided comprehensive NIS2 compliance consulting for a medium-sized technology solutions provider — from the initial assessment of compliance with Act No. 264/2025 Coll. and Decree No. 410/2025 Coll., through identification of critical gaps, to the implementation of technical and organizational measures. The result is auditable documentation and a network architecture ready for NÚKIB inspection.
Read article
Bloknet is an optical internet network built by New Telekom in the VBLOKU residential complex on Peroutkova Street in Prague 5. The project demonstrated that guaranteed symmetrical fiber optic FTTH connectivity — standardly available to corporate clients — can be fully delivered to every apartment. Activation within 48 hours, no FUP, no aggregation.
Read article
New Telekom implemented a dedicated private MPLS VPN link for a Czech manufacturer based in Prague between its headquarters in the Czech Republic and its branch in Shanghai — independent of the public internet, with guaranteed symmetrical capacity and SLA. The project demonstrates how an international Prague—Shanghai connection works in practice: from selecting transit operators and navigating China's regulatory specifics to 24/7 operational monitoring.
Read article
New Telekom delivered a complete network infrastructure for a technology company based in an office complex in Prague — Smíchov: guaranteed symmetrical B2B Internet 10 Gbit/s, a dedicated MPLS VPN private line to a Prague data center, a CloudConnect private circuit to Microsoft Azure, and a backup SD-WAN layer. Results: latency to NIX.CZ under 1.1 ms, latency to Azure West Europe under 7 ms, 99.9% SLA, and zero dependence on the public internet for critical traffic.
Read article
New Telekom s.r.o. delivered a comprehensive deployment of guaranteed symmetric B2B internet connectivity for a large multi-tenant administrative complex in Prague 4 — Michle. The project included FTTO fiber optic cabling, distribution network construction, installation of Juniper and Cisco active equipment, redundant backup connectivity via SD-WAN, and handover with a 99.9% SLA guarantee.
Read article
Connecting to Microsoft Azure or AWS over the public internet poses security, performance and legal risks in 2026. CloudConnect — New Telekom's private MPLS VPN service — replaces the public internet with a dedicated physical link offering guaranteed latency, isolation from DDoS attacks and savings of up to 50% on egress traffic.
Read article
On April 10, 2026, New Telekom Ltd. celebrates exactly 24 years since its registration as a limited liability company. Over that time, it has grown from a regional voice service provider into one of the key B2B telecommunications operators in the Czech Republic — with its own Juniper backbone network, membership in NIX.CZ and RIPE NCC, and interconnection with 120+ foreign operators.
Read article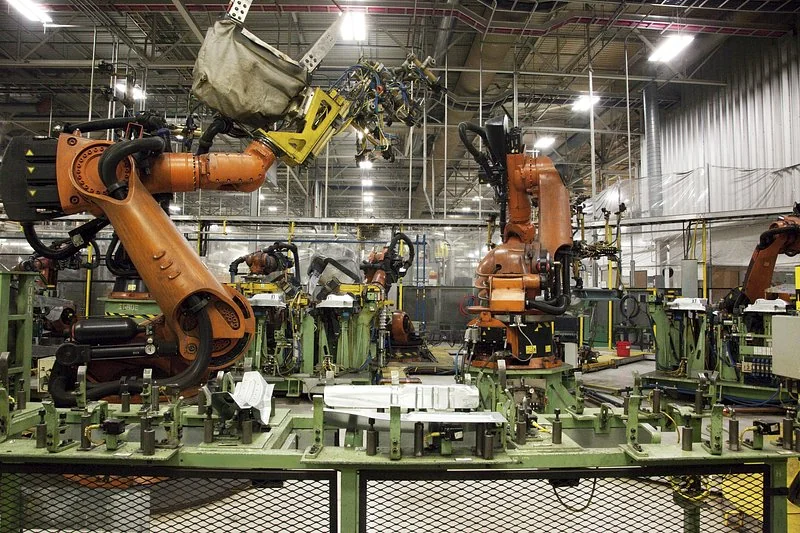
5G network slicing allows industrial enterprises to reserve a dedicated virtual network segment for critical machines and production lines — with guaranteed latency below 5 ms, traffic isolation and reliability of 99.999%. A guide for IT managers and operations directors of industrial plants and logistics centres.
Read article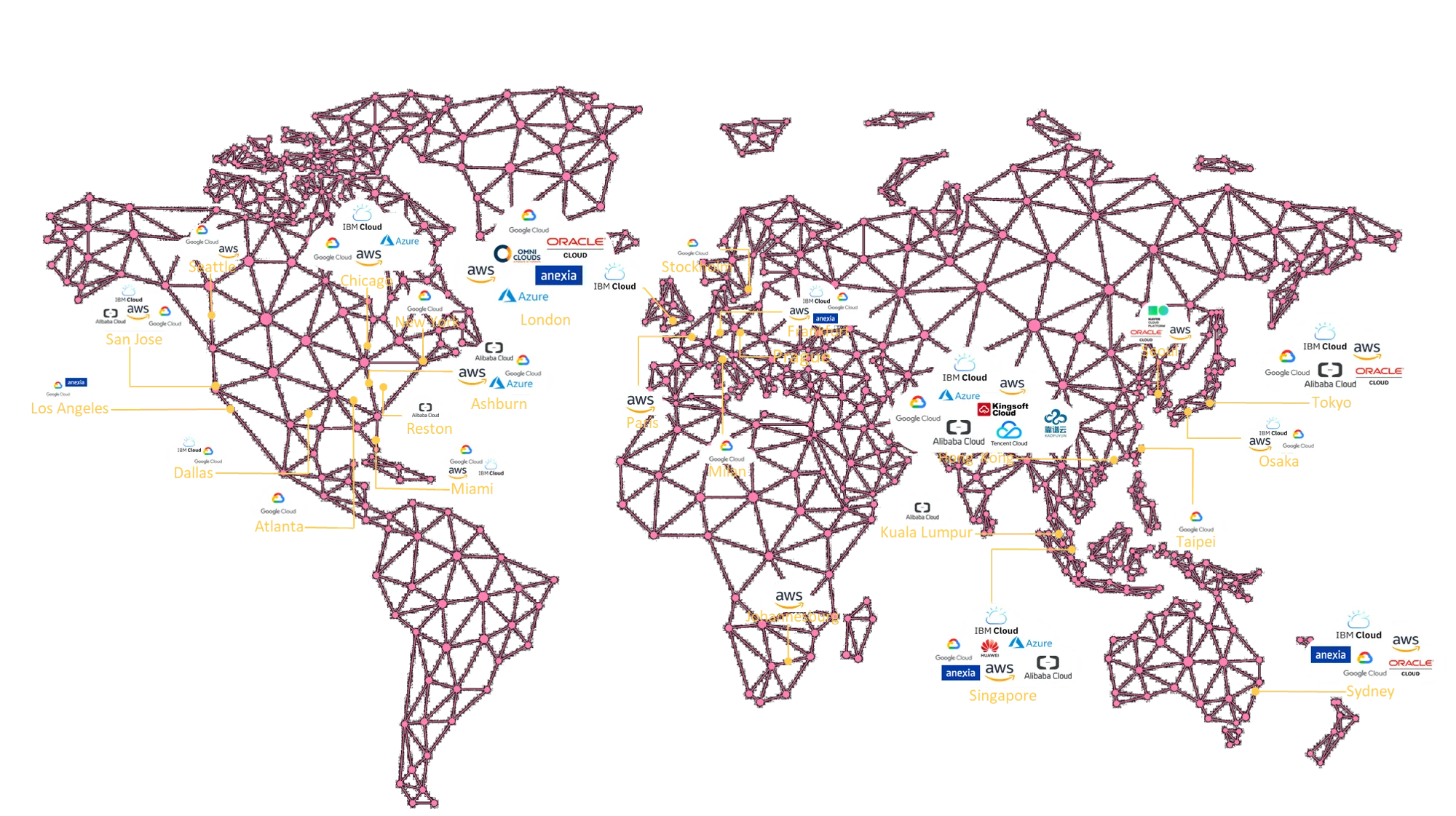
CloudConnect is a private VPN service built on MPLS VPN technology that connects enterprise networks to Public Clouds, Private Clouds and 500+ data centres without traversing the public internet. A guide for IT managers and security architects.
Read article
The NIS2 directive and the new Cyber Security Act are fundamentally changing the requirements for corporate connectivity. A guide to deploying SD-WAN, CloudConnect, and Zero Trust architecture to meet NÚKIB requirements.
Read article
Implementing guaranteed symmetric B2B internet connectivity in Prague 1 presents specific challenges that simply do not exist in modern office parks: heritage-protected buildings, medieval sewer networks, limited cable routes, and a ban on surface excavations. New Telekom delivered a dedicated FTTO 1 Gbit/s connection with a 99.9% SLA and redundant last mile for a corporate client in central Prague — without a single intervention into the facade of the historic building.
Read article